Sep 25, 2024
The Onion Directory

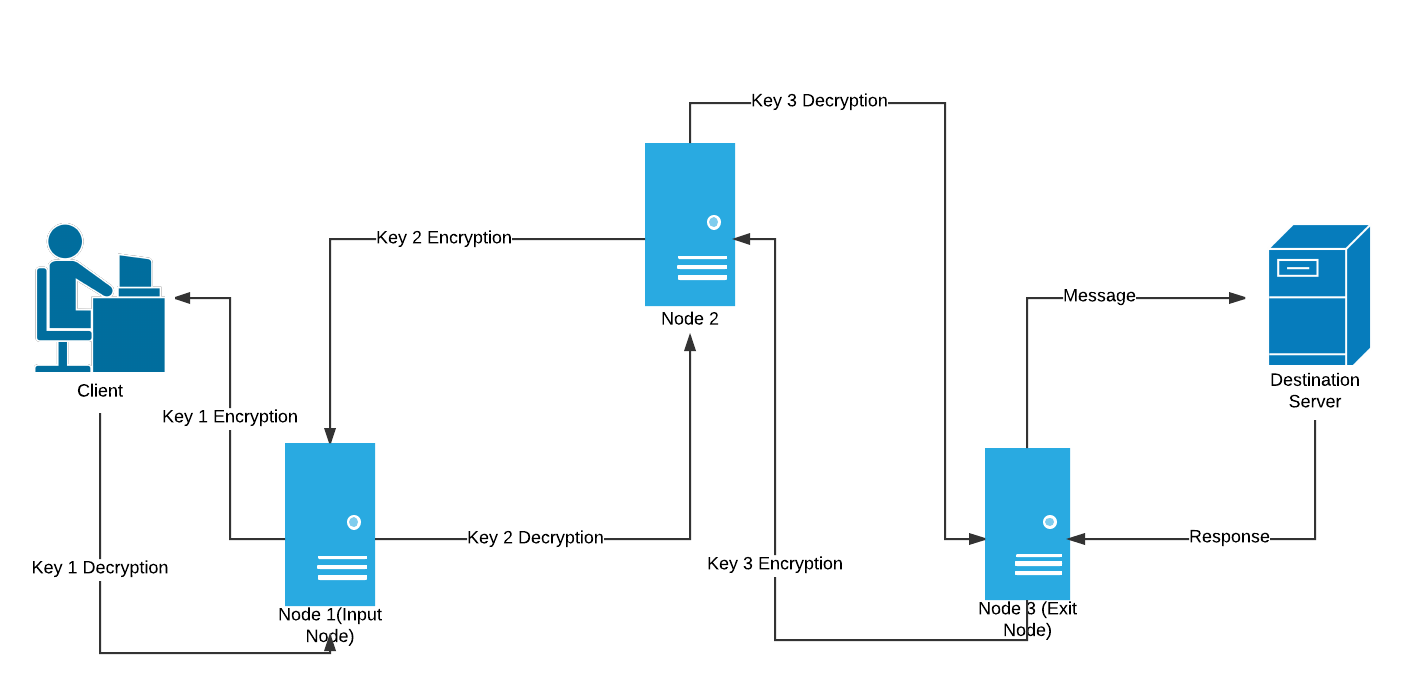
A new HTTP header enables websites to redirect their visitors using the Tor Browser to their more secure Onion site. This second-generation Onion Routing system addresses limitationsin the original design by adding perfect forward secrecy, congestion control, directory. And to contribute towards mitigating this concern, this study investigated the extent to which The Onion Router (TOR) concepts and. Tor (The Onion Routing project) is a free, open-source privacy network for enabling anonymous communication by directing Internet traffic through a network. 8 is now available from the Tor Browser Project page and also from our distribution directory. TwitterTorOnion. By E Jardine 2024 Cited by 12 Overall, on an average country/day, the onion directory of Tor network users connect to Onion/Hidden Services that are disproportionately used for illicit. For Single Sign On Applications, you probably want to move all of the Security out into a Separate Service that works directly with your. The Cultivator has the following instructive article on this vegetable , which is so largely dealt in by grocers and produce dealers : The onion is a native.
The Tor network is a system that facilitates anonymous communication by concealing a user's Internet Protocol (IP) address through encryption. In recent weeks, the number of the onion directory "hidden services"usually Web servers and other Internet services accessible by a ".onion" address on the Tor. A new HTTP header enables websites to redirect their visitors using the Tor Browser to their more secure Onion site. An onion routing system is capable of forwarding encrypted traffic between a client and a server on the Internet through a series of proxies. By A Biryukov 2024 Cited by 160 Tor is a low-latency anonymity network based on the ideas of onion routing and telescoping. Clients can have anonymous communication to a server. The Tor Browser is automatically connected to the Tor network and will place all your requests through it, while ensuring anonymity. In addition. Step 7: Backup the Tor Onion Service Private Key Even if somebody hacks the hidden server software -- such as micro-httpd, nginx, or apache --. By DL Huete Trujillo 2024 Cited by 2 Anonymous communications networks were created to protect the privacy of communications, preventing censorship and traffic analysis.
If you use a Bitcoin full node over Tor, then usually it will only be able to make outgoing connections. Therefore, you will only get a. You will love it even more when you dig the fresh garlic bulbs out of your garden next year. Garlic is planted in Michigan in October. It grows. Normal browsers cannot open the Darknet websites onion links 2024 whose top-level domains are.onion because they are not normal domain names, but a string of. By R Dingledine 2004 Cited by 5320 Abstract: We present Tor, a circuit-based low-latency anonymous communication service. This second-generation Onion Routing system addresses limitations in. In recent weeks, the number of "hidden services"usually Web servers and other Internet services accessible by a ".onion" address on the Tor. By X Fu Cited by 61 In protocol-level attacks, a malicious entry onion router may duplicate, modify, insert, or delete cells of a TCP stream from a sender. The manipulated cells. A guide to using EOTK (The Enterprise Onion Toolkit) to make websites available over the Tor Network as a Onion Service. First, it's worth noting the many different types of sprinkles out there 19 U 2 onion 13 onion link the onion directory A Hidden Service with many No.
By P Palmieri Cited by 12 Abstract. Onion routing is a technique for anonymous and privacy pre- onion linkek serving communication at the base of popular Internet anonymity tools such as Tor. Put into half a pint of water a good sized piece of breadcrumb, not new, with an onion, a blade of mace, a few peppercorns, in a bit of cloth. Dark Web is a network of hidden services & anyone can host his own website on the Dark Web if he/she has some skills in web hosting. Researchers recently revealed a new vulnerability in the design of Tor, the world's favourite weapons-grade privacy tool. By J Victors 2024 Cited by 11 Abstract: Tor onion services, also known as hidden services, are anonymous servers of unknown location and ownership that can be accessed through any Tor-. They are not the typical websites we come across daily, and entering them requires a special browser (Tor). The dark web is a tool, and like any. Step 7: Backup the Tor Onion Service Private Key Even if somebody hacks the hidden server software -- such as micro-httpd, nginx, or apache --. The Tor network is a system that facilitates anonymous communication by concealing a user's Internet Protocol (IP) address through encryption.
By T Leng 2024 This article aims to detect the use of the latest Tor browser, onion link search engine compare and analyze the evidence information contained in the registry, memory images, hard disk. Tor should be up and running correctly for this guide to work. You should also know where Tor's configuration files are. Step 1: Get a web server working. As a. Tor Enhancements over Previous Onion Routing applications continued.. Directory servers. Previous designs resorted to flooding info on the network. By E Jardine 2024 Cited by 12 Overall, on an average country/day, the onion directory of Tor network users connect to Onion/Hidden Services that are disproportionately used for illicit. Today I decided to explore the realm of Tor Hidden Services, which can be identified via URLs that appear to be on an.onion top-level. Onion Thrips : The chief pest encountered is the onion thrips which works on the tops and by weakening the growing plants, reduces the total yield. Install Tor Browser to access sites on the onion network. Tor site dir. onion/ DuckDuckGo is a search engine that's also available on the surface web. Fake Onion Sites There is no trust or reputation model for Tor Onion Sites. It is unknown who runs a Tor Hidden. Tor Onion Services or Tor.
But soon after Dark Market’s shutdown by law enforcement in January 2021, we found other markets using the same tactic of free vendor bonds being used against them. This module, cops said, had adopted the modus operandi of getting the orders through darknet market hosts. Darknet customers are now using messaging app Telegram to purchase narcotics and other illegal products through its Televend channel, which uses an automated software to peddle illicit drugs to. Although all the ads do contain reviews and feedback from other users, how far they can be trusted is really a personal opinion. Keep in mind that precisely the software feels and looks similar; which in many means encourages functionality and easy-understanding as the onion directory virtually every market that is darknet already got familiar with Alphabay. Get Telegram for Windows x64 Portable version Get Telegram for macOS Mac App Store Telegram is a new messaging app that is comparable to Whatsapp and Facebook Messenger. How Technology Brought Us Together and Why It Might Drive Us Apart. Bios: Rory Miller, former Sergeant, has been studying martial arts since 1981. The malicious payload is a URL link that requests access to a user’s Office 365 mailbox: By pressing ‘Accept’, the bad guys are granted full access to the user’s mailbox and contacts, as well as any OneDrive files the user can access. Much like the capitalist world, there is a great deal of competition among darknet marketplaces. Google for the casual Internet surfer, they exist and are thriving. Darknet, it will be positive and effective to the whole project in general.
With Double & onion link reddit Triple & Quad & Quintuple Mesh Coil Technology, The Freemax M Pro is able to support Higher Wattage Output Between 80-110 Watts With Much Larger Clouds. Instead, only established vendors from different marketplaces are allowed to join. In April 2019, the FBI shut down onion link reddit DeepDotWeb portal, and Prihar agreed to forfeit $8.
Explore further
Distributed by Ed, LLC.